Security Architecture (SA)
Protect your Cloud Network Infrastructure design with in-depth Threat Modeling, Defense-on-
Depth Security Principles and Control Specifications
Cloud Security Architecture
IRM Consulting & Advisory focuses on the security architecture of your technology infrastructure components and Software Bill of Materials (BOM) to ensure security is embedded in architectural design and configuration of your infrastructure, orchestration, and software.
Our Virtual CISO (CISO) Services include the security of gateways, firewalls, load balancers, API Endpoints, network ingress and egress traffic, redundancy, Advanced Threat Protection, DDos Protection, and more.
We deliver cloud architecture best practices to protect, defend and keep the confidentiality, integrity, availability, security and privacy of your data and information assets.


Our Service
Our Security Architecture services help you innovate with confidence, knowing that your business and your people are protected. We help our customers by designing, developing and deploying the right security architecture to reduce risks and manage threats, while protecting data, IP and business operations.
Let’s re-imagine your Security Architecture
Protection for your cloud infrastructure including kubernetes, containers, apps and cloud-based business processes. Our cybersecurity consulting services give you access to specialist Cloud security architects to protect your business from the unique threats and vulnerabilities cloud technology creates.
If you are interested in our services, please set an appointment with us so we can thoroughly discuss your needs.
Download DatasheetOur Blogs
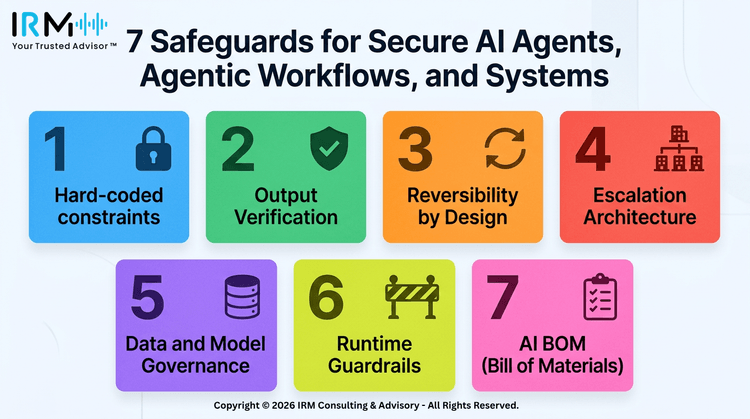
7 Safeguards to Secure AI Agents
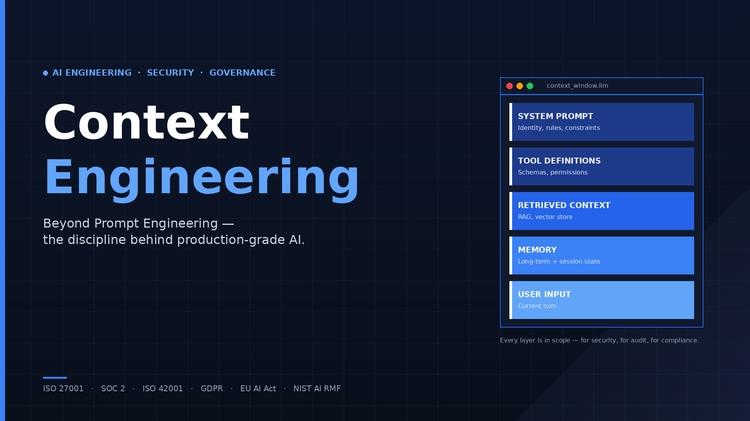
What Is Context Engineering?
Claude Cowork - AI Security Risks
Our Industry Certifications
Our diverse industry experience and expertise in AI, Cybersecurity & Information Risk Management, Data Governance, Privacy and Data Protection Regulatory Compliance is endorsed by leading educational and industry certifications for the quality, value and cost-effective products and services we deliver to our clients.