Frequently Asked Questions - FAQ's
We answer questions about our Virtual (vCISO) Services


Frequently Asked Questions (FAQs) for Virtual CISO (vCISO) Services in Canada
A Penetration Test, also known as a Pen Test, is a simulated cyberattack against your Web Application or System Infrastructure and Network to check for exploitable vulnerabilities. Pen Testing aims to identify vulnerabilities and risks which may negatively impact the Confidentiality, integrity, Availability, Security and Privacy of data and information assets.
Threat modeling is a process by which potential threats, such as structural vulnerabilities or the absence of appropriate safeguards, can be identified, enumerated, and mitigations can be prioritized.
Ransomware is malicious software (malware) used in a cyberattack to encrypt the victim’s data with an encryption key that is known only to the attacker, thereby rendering the data unusable until a ransom payment (usually cryptocurrency, such as Bitcoin) is made by the victim.
Ransomware is not a new threat. The earliest known ransomware, known as PC Cyborg, was unleashed in 1989. Since that time, ransomware has evolved and become far more sophisticated.
Ransomware has also become more pervasive and lucrative with developments such as the following:
- Ongoing digital transformation: As more organizations digitize their operations and employees use email, cloud apps, and mobile devices to get work done, the number of potential entry points for attackers increases exponentially. After a network has been breached, infections can spread more quickly when critical systems are connected.
- The rise of cryptocurrency: Currency (such as Bitcoin) enables easy and virtually untraceable payments to anonymous cybercriminals. As cryptocurrency speculation continues to push prices higher, the potential for large ransoms grows proportionally.
- The emergence of Ransomware-as-a-Service (RaaS): RaaS (ransomware that can be purchased for a small fee and/or a percentage of the ransom payment) makes it easy for practically anyone to use ransomware which is concerning.
No - That's why a vCISO Service is ideal, we cater for small businesses who are most vulnerable to cyberattacks. Our Virtual CISO Services provide enterprise-grade cybersecurity & AI Risk Management expertise without a $250K+ salary of a Full-Time CISO.
Our Virtual CISO (vCISO) engagements are designed to reduce cost over time as we improve your cybersecurity posture and maturity over-time.
Yes- Absolutely!
This is one of the key pain points for scaling SaaS companies, A Virtual CISO wins you new customers and enhances your conversion rates by providing the right responses to security questionnaires.
An AI-Native vCISO understands cyber risk management, and also understands the risks associated with the use and development of LLMs, AI tools, applicaitons and systems. An AI-Native vCISO conducts AI Risk Assessments by including ISO42001, NIST RMF and AI Regulatory requirements into the assessment scope.
A formal Security Incident Response Plan (IRP) is not paperwork—it's your battle rhythm for turning Cybsersecuity Incidents and Data Breaches into damage limitation with a controlled and timely recovery. In the event of a Cyber incident or Data Breach, an IRP helps organizations orchestrate everything in between so you contain damage fast, communicate credibly, meet legal deadlines, and preserve customer trust and revenue.
Businesses without a Formal and tested IRP face these risks - 2–5× longer recovery, 30–60% higher costs, regulatory penalties, legal costs, 20–50% customer churn, potential loss of enterprise deals, and existential business risk.
A cybersecurity program is a documented set of your organization’s information security policies, procedures, guidelines, standards and operating procedures. The security program utilizes an industry-standard security framework and includes a roadmap, plan and milestones for effective implementation of security management best practices and controls.
Security is about the safeguarding of data, whereas Data privacy is about proper usage, collection, retention, deletion, and storage of personally identifiable or health information inline with Privacy Laws and Data Protection Regulations.
Data Security is about protection against the unauthorized access and disclosure of data. Encryption is typically used as a security control to mitigate this risk.
Email security is the process of ensuring the availability, integrity and authenticity of email communications by protecting against the risk of email threats.
"With over 90% of attacks on organizations starting from a malicious email, relying on your built-in security might leave your organization open to cyber criminals that constantly capitalize on the number one attack vector: exploiting human nature and the lack of tight security.
- The Phishing Threat
A phishing email is designed to use social engineering to exploit your organization’s employees. If an attacker can get a user to click on a malicious link or open an infected attachment, they can steal login credentials and other personal data or install malware on the employee’s computer. From there, the cybercriminal can expand their access on the corporate network to steal sensitive data or perform other attacks.
Over 90% of cyberattacks begin with a phishing email, and the reason for this is that phishing emails are effective. It is often much easier to convince an employee that they need to take action on their Netflix account or send a payment to a vendor than to identify and exploit a vulnerability in a company’s systems.
- Exploiting Cloud Email
The rapid adoption of cloud computing has only made it easier for cybercriminals to exploit email. The growing use of cloud-based email and document sharing solutions – such as Google Drive and Microsoft 365 – have opened up new attack vectors for cybercriminals.
An attacker will commonly send a phishing email masquerading as a legitimate shared document. Upon clicking on the link, the target will be prompted to enter their credentials for the service to view it, which sends these credentials to the attacker. If the organization has not configured their cloud infrastructure to provide visibility into account usage and implement access control, an attacker can use these stolen credentials to access sensitive data throughout the company’s cloud.
6 Months
An experienced Virtual CISO can prepare your business for SOC2 Type II or ISO27001 Certification in 6 months at 40% less cost.
A Virtual CISO is 40% less cost than a full-time CISO. A Vitual CISO aligns Cybersecurity with your Business Strategy. A Virtual CISO does not spend time managing people, instead they focus thier time on quantifying and reducing risks to improve your cybersecurity posture and maturity
Our Approach to your Cybersecurity Assurance
& AI Governance
Our consultative approach is simple, yet highly effective for small businesses. We have a simple five (5) step process towards guiding your business to achieving the information security posture and maturity level that is aligned to your business goals, objectives and risk appetite.
Discover Critical Assets
Assess Risk and Impact
Prioritize based on Risk
Mitigate with Effective Solutions
Ongoing Assurance and Sustainability
Client Testimonials
We tailor and right-size our Services that align to our Clients current business goals and with future growth in mind.
Our Blogs
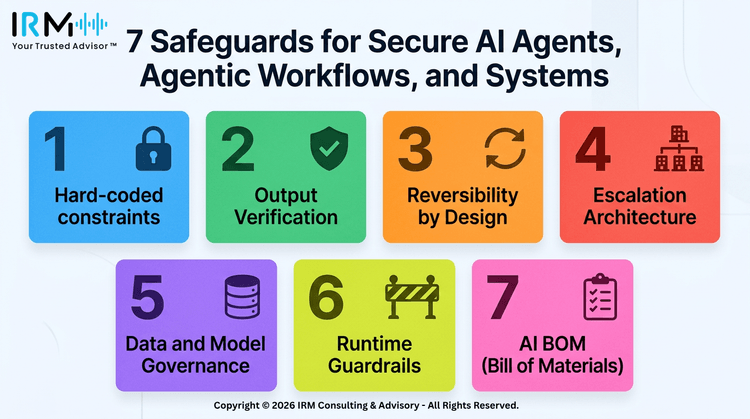
7 Safeguards to Secure AI Agents
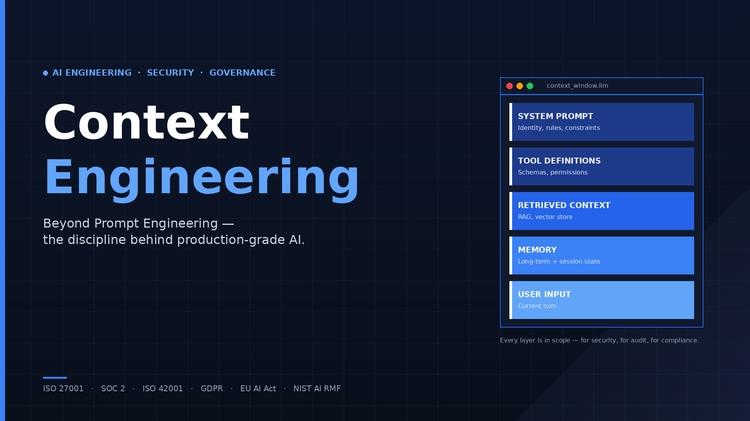
What Is Context Engineering?
Claude Cowork - AI Security Risks
Our Industry Certifications
Our diverse industry experience and expertise in AI, Cybersecurity & Information Risk Management, Data Governance, Privacy and Data Protection Regulatory Compliance is endorsed by leading educational and industry certifications for the quality, value and cost-effective products and services we deliver to our clients.