Governance Risk & Compliance (GRC)
Govern, Manage Risk and ensure Compliance and sustainability of your Security Program
What is Governance, Risk & Compliance) (GRC)
Are you using spreadsheets or task management tools to manage you Security Governance, Risk and Compliance? Are your security management and reporting processes very manual, time-consuming with a lot of effort?
Governance, Risk, and Compliance (GRC) is an integrated framework that aligns an organization's security governance structure, risk management processes, and regulatory compliance obligations into a single, managed program.
For SaaS companies Startups and SMB's, a managed GRC platform replaces fragmented spreadsheets and manual processes with automated evidence collection, continuous control monitoring, and audit-ready reporting. Supported with Virtual (vCISO) Services to meet today’s complex cyber risks while aligning with industry best practices, regulations, and compliance mandates.
Automate Risk Management and Compliance
Accelerate the governance of your Cybersecurity Risk & Compliance program on one Platform with frameworks to help your business align its information security, compliance requirements, risk and controls with your business objectives.
Perform Control Assessments across multiple frameworks
Implement and assess new security frameworks, such as SOC2, ISO 27001, PCI DSS, CMMC, and others. Easily access templates that include a framework’s requirements and controls to assess including access to our Virtual CISO advisory services
Centralize Risk Assessments and Risk Management Processes
Adopt and manage leading risk management frameworks and strategies through risk assessment and mitigation. Consolidate all risk data, control implementations, and compliance measures in a single platform, facilitating streamlined monitoring and effective management of enterprise risks.
Develop, manage and communicate Policies and Procedures
Security assessments always involve an auditor’s review of your company’s current security policies, incident response plan, business continuity plan, privacy policies, and other documents. Develop and integrate policies and procedures into one place so the latest versions of company policies and key documents can be communicated automatically.
Manage Third-Party and Supply Chain Risks
Manage all of your vendors and easily assess vendors’ security and compliance posture -- all within one platform. Maintain a central register of critical vendors, including contracts, vendor risk assessment questionnaires, and internal control activities to mitigate vendor risk. Assess each vendor’s security and compliance posture through customizable questionnaires. Easily leverage questionnaire responses as evidence of compliance measures.
Certification Readiness and Audit Management
Workloads have increased exponentially in the recent years as customers make heavy demands of their vendors to provide security assurance. Our GRC Platform can help to reverse this alarming trend and prevent burnout by automating and streamlining common workflows allowing you to collaborate seamlessly for your SOC2 and ISO27001 certification readiness and Internal/External Audits.
If you are interested in our Cybersecurity Consulting Services, please set an appointment with us so we can thoroughly discuss your needs.
Download DatasheetOur Blogs
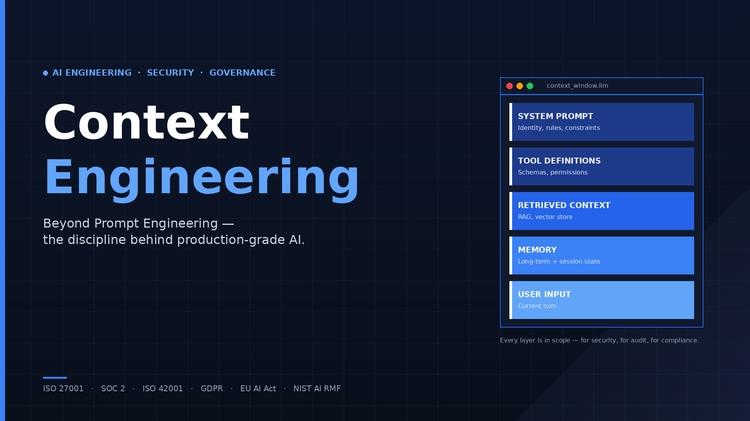
What Is Context Engineering?
Claude Cowork - AI Security Risks
Cyber Risks that quietly kill Healthcare PE Firms
Our Industry Certifications
Our diverse industry experience and expertise in AI, Cybersecurity & Information Risk Management, Data Governance, Privacy and Data Protection Regulatory Compliance is endorsed by leading educational and industry certifications for the quality, value and cost-effective products and services we deliver to our clients.